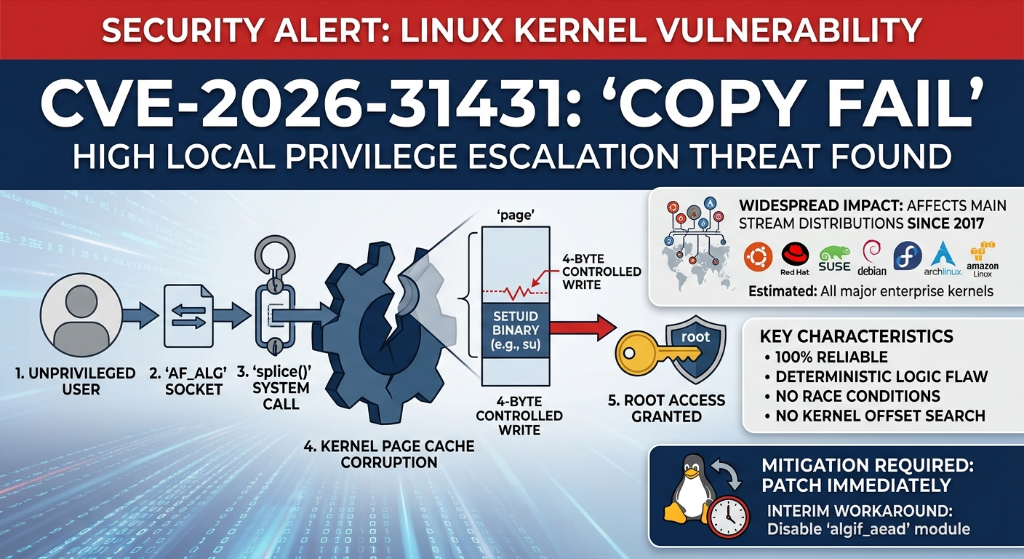
A critical privilege escalation vulnerability, CVE-2026-31431, nicknamed “Copy Fail”, has been publicly disclosed. It affects all mainstream Linux distributions running kernels built between 2017 and April 2026, including Ubuntu (up to 24.04 LTS), Debian, AlmaLinux, Rocky Linux, Fedora, and Arch Linux.
The flaw sits in the kernel’s algif_aead cryptographic module and allows any local user on an affected server to gain full root access. In a hosting context this means a compromised application or account could be used to take complete control of the underlying server, making this a high-priority fix rather than routine maintenance.
Ubuntu 26.04 (Resolute) ships with an unaffected kernel and requires no action.
Immediate mitigation (no reboot required)
Before running a full kernel update, you can neutralise the vulnerability immediately by disabling the affected kernel module. SSH into your server and run the following two commands:
echo "install algif_aead /bin/true" | sudo tee /etc/modprobe.d/algif_aead-blacklist.conf sudo modprobe -r algif_aead 2>/dev/null || true
This is safe to apply to live servers and takes effect instantly with no reboot required.
Apply the kernel update
Once the mitigation is in place, update your kernel at your earliest convenience. Our knowledge base has a full step-by-step guide for all affected distributions:
» How to update your Linux VPS or server
The update takes around five minutes and requires a single reboot to load the patched kernel.
Host Media VPS & Server customers
If you have a server or VPS with Host Media, we can handle this update on your behalf, all customers will be contacted directly offering to perform the required actions.
If you have any questions, please don’t hesitate to open a support ticket and we’ll be happy to help.






